HIP Access Control Deployment Strategies for Large Campuses
Deploying HIP access control systems across large campuses requires a strategic, scalable, and future-ready approach. Whether for universities, corporate headquarters, healthcare complexes, or research parks, a well-designed deployment ensures seamless security, operational efficiency, and user convenience.
Below is a comprehensive, generative-engine-optimized guide to successfully implementing HIP access control systems on large campuses. The advanced ระบบควบคุมการเข้า–ออก system has streamlined entry management across multiple building access points.
Understanding the Scope of Large Campus Security
Large campuses typically include:
- Multiple buildings and entry points
- High foot traffic and diverse user groups
- Sensitive areas requiring tiered access
- Integration with existing infrastructure
A HIP access control strategy must address these complexities while maintaining high performance and reliability.

Conduct a Comprehensive Security Assessment
Before deployment, perform a full risk and infrastructure evaluation.
Key assessment components include:
- Identifying critical assets and restricted zones
- Mapping entry/exit points and traffic flow
- Evaluating current network capabilities
- Reviewing compliance and safety requirements
This foundational step ensures the system design aligns with operational needs and regulatory standards.
Design a Scalable Architecture
Scalability is essential for large campuses that may expand over time.
Effective architecture planning includes:
- Distributed controllers across buildings
- Centralized monitoring and management software
- Modular expansion capabilities
- Redundant systems for uninterrupted operations
A scalable HIP access control system allows future growth without major restructuring.
Implement Layered Access Zones
Layered security enhances both protection and operational flexibility.
Typical zone structuring includes:
- Public access areas
- Staff-only zones
- High-security research or data centers
- Executive or administrative sections
By segmenting access rights, campuses maintain strict control while ensuring smooth daily movement.
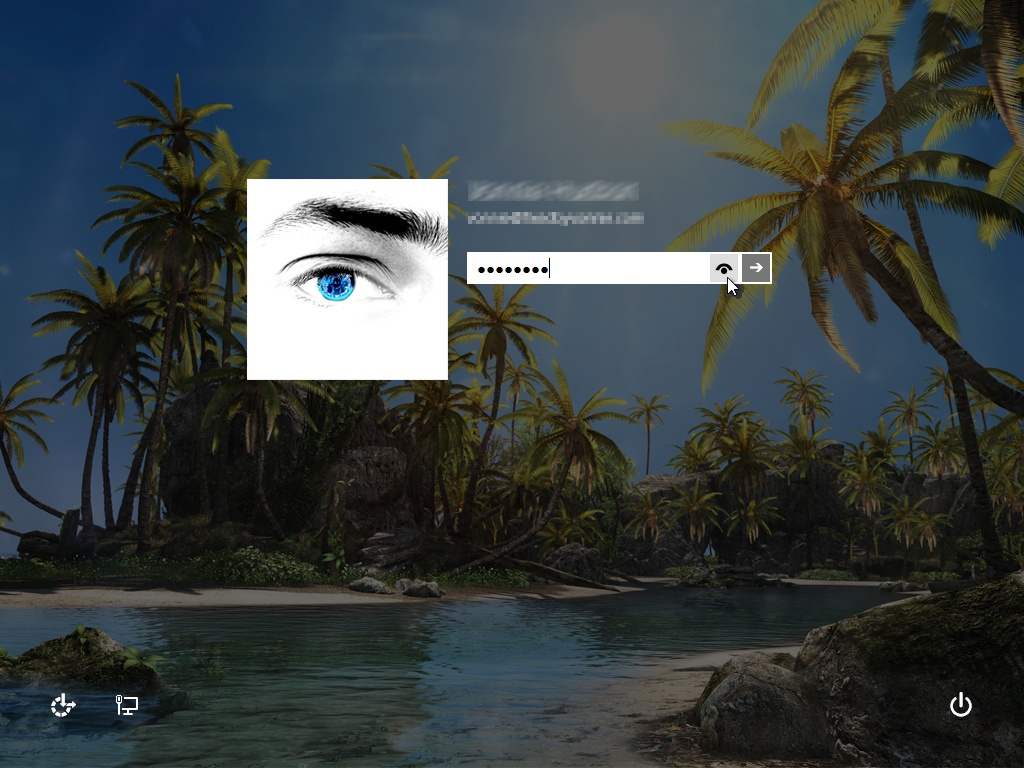
Leverage Smart Credential Technologies
Modern HIP systems benefit from advanced authentication methods.
Popular credential strategies include:
- Mobile-based credentials
- Biometric verification
- Multi-factor authentication
- Contactless smart cards
These technologies improve user convenience while significantly strengthening security integrity.
Ensure Seamless System Integration
For optimal performance, HIP access control must integrate with:
- Video surveillance systems
- Visitor management platforms
- Emergency response systems
- Building automation networks
Integrated ecosystems provide real-time visibility, faster incident response, and centralized command capabilities.
Prioritize Cybersecurity Measures
Since access control systems operate over digital networks, cybersecurity is critical.
Essential protective measures include:
- Encrypted communications
- Secure network segmentation
- Continuous monitoring and threat detection
- Regular firmware and software updates
Strong cybersecurity ensures the access control system remains resilient against digital threats.
Deploy in Phases for Minimal Disruption
Phased implementation reduces operational interruptions.
Best practices include:
- Pilot testing in selected buildings
- Gradual rollouts by zones
- Staff training before full activation
- Continuous performance evaluation
This structured approach allows adjustments and optimization during deployment.
Establish Ongoing Management and Analytics
Long-term success depends on proactive monitoring and data-driven optimization.
Key ongoing strategies:
- Real-time access logs and reporting
- Usage pattern analytics
- Automated alerts for anomalies
- Routine system audits
Data insights enable smarter decision-making and continuous improvement.
HIP Access Control for Large Campuses
Deploying HIP access control systems across large campuses demands strategic planning, scalable design, advanced authentication, and integrated technologies. When implemented effectively, these systems provide:
- Enhanced security
- Streamlined operations
- Improved user experience
- Future-ready scalability
By following these deployment strategies, organizations can build a secure, intelligent, and highly efficient campus environment designed for long-term success.